
- Home
- Course
- IT & Software
- CompTIA CySA+ Cybersecurity Analyst Course
CompTIA CySA+ Cybersecurity Analyst Course
Embark on a transformative journey with the “CompTIA CySA+ Cybersecurity Analyst Course,” designed to fortify the digital frontiers of business. This comprehensive training program begins with an immersive introduction to the cybersecurity realm, setting the stage for a deep dive into the sophisticated world of threat data and intelligence. With an emphasis on real-world application, participants will gain invaluable insights into organizational security, developing the acumen to anticipate, identify, and neutralize digital threats. Mastery over vulnerability assessment tools and mitigation strategies forms the bedrock of this curriculum, providing learners with a robust skill set pivotal for the modern cybersecurity landscape.
Learning Outcomes
- Interpret threat data to reinforce organizational security frameworks.
- Assess vulnerabilities using state-of-the-art tools and methodologies.
- Apply best practices for ensuring software and hardware assurance.
- Analyze security solutions for robust infrastructure management.
- Implement and manage incident response protocols to address potential compromises effectively.
Why choose this CompTIA CySA+ Cybersecurity Analyst Course?
- Unlimited access to the course for a lifetime.
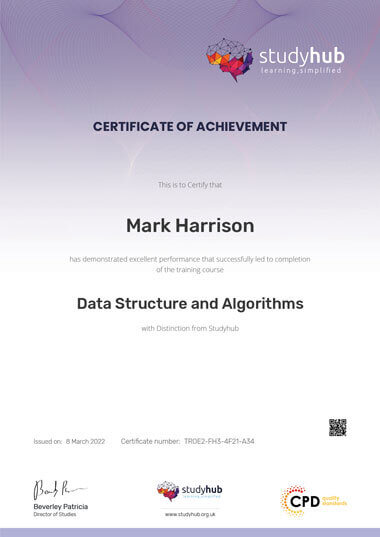
- Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course.
- Structured lesson planning in line with industry standards.
- Immerse yourself in innovative and captivating course materials and activities.
- Assessments are designed to evaluate advanced cognitive abilities and skill proficiency.
- Flexibility to complete the CompTIA CySA+ Cybersecurity Analyst Course Course at your own pace, on your own schedule.
- Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience.
Who is this CompTIA CySA+ Cybersecurity Analyst Course for?
- Individuals aiming to specialize in cybersecurity analysis.
- IT professionals seeking to broaden their cybersecurity knowledge.
- Organizational staff responsible for managing digital security risks.
- Security consultants requiring up-to-date threat intelligence expertise.
- System administrators looking to implement enhanced security measures.
Career path
- Cybersecurity Analyst – £25,000 to £60,000
- Vulnerability Analyst – £30,000 to £65,000
- Security Operations Centre (SOC) Analyst – £32,000 to £70,000
- Incident Responder – £27,000 to £68,000
- Digital Forensics Specialist – £35,000 to £75,000
- Information Security Consultant – £40,000 to £80,000
Prerequisites
This CompTIA CySA+ Cybersecurity Analyst Course does not require you to have any prior qualifications or experience. You can just enrol and start learning.This CompTIA CySA+ Cybersecurity Analyst Course was made by professionals and it is compatible with all PC’s, Mac’s, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection.
Certification
After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8.
Course Curriculum
| Section 01: Introduction | |||
| Introduction | 00:02:00 | ||
| All about the Exam | 00:08:00 | ||
| What’s New on the CompTIA CySA+ Exam? | 00:05:00 | ||
| Meet the Instructors | 00:02:00 | ||
| Thinking like the Enemy | 00:09:00 | ||
| Section 02: The Importance of Threat Data and Intelligence | |||
| Intelligence Sources and Confidence Levels | 00:08:00 | ||
| Threat Indicators and Actors | 00:08:00 | ||
| Threat Trends | 00:07:00 | ||
| Intelligence Cycle and ISACs | 00:06:00 | ||
| Section 03: Threat Intelligence in Support of Organizational Security | |||
| Attack Frameworks | 00:06:00 | ||
| Threat Research | 00:11:00 | ||
| Threat Modeling and Intelligence Sharing | 00:06:00 | ||
| Section 04: Vulnerability Assessment Tools | |||
| Vulnerability Identification | 00:07:00 | ||
| Scanning Parameters and Criteria | 00:09:00 | ||
| Scanning Special Considerations | 00:06:00 | ||
| Validation | 00:03:00 | ||
| Remediation and Mitigation | 00:08:00 | ||
| Inhibitors to Remediation | 00:07:00 | ||
| Section 05: Threats and Vulnerabilities Associated with Specialized Technology | |||
| Web Applications Scanners, Part 1 | 00:10:00 | ||
| Web Applications Scanners, Part 2 | 00:05:00 | ||
| Scanning | 00:06:00 | ||
| Configuring and Executing Scans | 00:08:00 | ||
| Vulnerability Scanning | 00:10:00 | ||
| Reverse Engineering | 00:08:00 | ||
| Enumeration | 00:06:00 | ||
| Wireless Assessment Tools | 00:08:00 | ||
| Cloud Assessment Tools | 00:04:00 | ||
| Section 06: Threats and Vulnerabilities Associated with Specialized Technology | |||
| Mobile and IoT | 00:10:00 | ||
| Embedded and Firmware Systems (RTOS, SoC, and FPGA) | 00:09:00 | ||
| Access and Vehicles Risk | 00:08:00 | ||
| Automation and Control Risk | 00:10:00 | ||
| Section 07: Threats and Vulnerabilities Associated with Operating in the Cloud | |||
| Cloud Models | 00:07:00 | ||
| Remote Service Invocation (FaaS, IaC, API) | 00:10:00 | ||
| Cloud Vulnerabilities | 00:06:00 | ||
| Section 08: Mitigating Controls for Attacks and Software Vulnerabilities | |||
| Injection and Overflow Attacks | 00:09:00 | ||
| Authentication Attacks | 00:07:00 | ||
| Exploits | 00:08:00 | ||
| Application Vulnerabilities, Part 1 | 00:08:00 | ||
| Application Vulnerabilities, Part 2 | 00:07:00 | ||
| Section 09: Security Solutions for Infrastructure Management | |||
| Network Architecture and Asset Management | 00:09:00 | ||
| Protecting Your Territory | 00:05:00 | ||
| Identity and Access Management | 00:11:00 | ||
| Encryption and Active Defense | 00:08:00 | ||
| Section 10: Software Assurance Best Practices | |||
| Platforms | 00:07:00 | ||
| SOA and DevSecOps | 00:09:00 | ||
| Secure Software Development | 00:08:00 | ||
| Best Coding Practices | 00:04:00 | ||
| Section 11: Hardware Assurance Best Practices | |||
| Trusted Hardware | 00:10:00 | ||
| Hardware Encryption | 00:04:00 | ||
| Hardware Security | 00:08:00 | ||
| Section 12: Data Analysis in Security Monitoring Activities | |||
| Data Analytics | 00:10:00 | ||
| Endpoint Security | 00:08:00 | ||
| Recon Results, Part 1 | 00:13:00 | ||
| Recon Results, Part 2 | 00:05:00 | ||
| Impact Analysis | 00:05:00 | ||
| Collective Tools | 00:09:00 | ||
| Query Writing | 00:07:00 | ||
| E-mail Analysis, Part 1 | 00:10:00 | ||
| E-mail Analysis, Part 2 | 00:08:00 | ||
| Section 13: Implement Configuration Changes to Existing Controls to Improve Security | |||
| Permissions | 00:09:00 | ||
| Firewalls | 00:08:00 | ||
| Intrusion Prevention Rules | 00:05:00 | ||
| DLP and Endpoint Detection | 00:05:00 | ||
| Section 14: The Importance of Proactive Threat Hunting | |||
| Threat Hunting and the Hypothesis | 00:06:00 | ||
| Threat Hunting Process | 00:07:00 | ||
| Results and Benefits | 00:05:00 | ||
| Section 15: Compare and Contrast Automation Concepts and Technologies | |||
| Workflow and Scripting | 00:07:00 | ||
| API and Malware Signature Creation | 00:08:00 | ||
| Threat Feeds and Machine Learning | 00:06:00 | ||
| Protocols, Standards, and Software Engineering | 00:05:00 | ||
| Section 16: The Importance of the Incident Response Process | |||
| IR Roles and Responsibilities | 00:08:00 | ||
| IR Active Preparation | 00:10:00 | ||
| Section 17: Appropriate Incident Response Procedures | |||
| Incident Response Process | 00:07:00 | ||
| Section 18: Analyze Potential Indicators of Compromise | |||
| Network Symptoms | 00:04:00 | ||
| Host Symptoms | 00:08:00 | ||
| Application Symptoms | 00:04:00 | ||
| Section 19: Utilize Basic Digital Forensics Techniques | |||
| Digital Forensics | 00:10:00 | ||
| Seizure and Acquisitions | 00:05:00 | ||
| Forensics Acquisition Tools | 00:09:00 | ||
| Mobile, Virtualization, and Cloud | 00:06:00 | ||
| Forensics Analysis, Part 1 | 00:04:00 | ||
| Forensics Analysis, Part 2 | 00:08:00 | ||
| Packet Capture | 00:12:00 | ||
| Section 20: The Importance of Data Privacy and Protection | |||
| Data Privacy and Security | 00:06:00 | ||
| Nontechnical Controls | 00:09:00 | ||
| Technical Controls | 00:08:00 | ||
| Section 21: Security Concepts in Support of Organizational Risk Mitigation | |||
| Business Impact Analysis | 00:05:00 | ||
| Risk Identification | 00:05:00 | ||
| Risk Calculation and Communication | 00:06:00 | ||
| Training | 00:04:00 | ||
| Supply Chain Assessment | 00:04:00 | ||
| Section 22: The Importance of Frameworks, Policies, Procedures, and Controls | |||
| Frameworks | 00:13:00 | ||
| Policies and Procedures | 00:05:00 | ||
| Controls and Procedures | 00:08:00 | ||
| Verification | 00:06:00 | ||
| Assignment | |||
| Assignment – CompTIA CySA+ Cybersecurity Analyst Course | 00:00:00 | ||
| Order your Certificate | |||
| Order your Certificate | 00:00:00 | ||

Related Courses
Overview Learn about from industry experts and boost your professional skill. This course will enhance your skill and make you ready …
1
In the ever-evolving digital landscape, the ability to understand, identify, and secure vulnerabilities in a Web Application has never been …
0
In today’s digital-first world, computer know-how is more than just a perk—it’s a necessity. Our Basic Computer Literacy Training opens …
1
Grab This Course for
$557.70 Original price was: $557.70.$26Current price is: $26. ex Vat
-
 Level: Intermediate
Level: Intermediate
-
 Duration: 11 hours, 25 minutes
Duration: 11 hours, 25 minutes -
 Students: 70
Students: 70
.png)









 (1) (1).png)