- Home
- Course
- IT & Software
- IT Administration and Networking
IT Administration and Networking
Embark on a transformative journey into the digital realm with “IT Administration and Networking“, a meticulously structured course designed to elevate your digital competencies. This educational adventure commences with an exploration of fundamental IT literacy, establishing a solid foundation for the inquisitive mind. The curriculum advances, navigating through the complexities of software management and hardware understanding. As you traverse the terrain of cybersecurity, you’ll become adept at safeguarding digital ecosystems against burgeoning threats. Concluding with a foray into the interconnected world of networking, the programme synthesises each element into a cohesive skill set that is indispensable in today’s technologically driven landscape.
Learning Outcomes
- Acquire foundational knowledge in IT concepts and operations.
- Gain insights into software configuration and troubleshooting.
- Understand hardware components and their interplay in computing systems.
- Master the principles of digital security and data protection.
- Grasp the essentials of constructing and managing network infrastructures.
Why choose this IT Administration and Networking course?
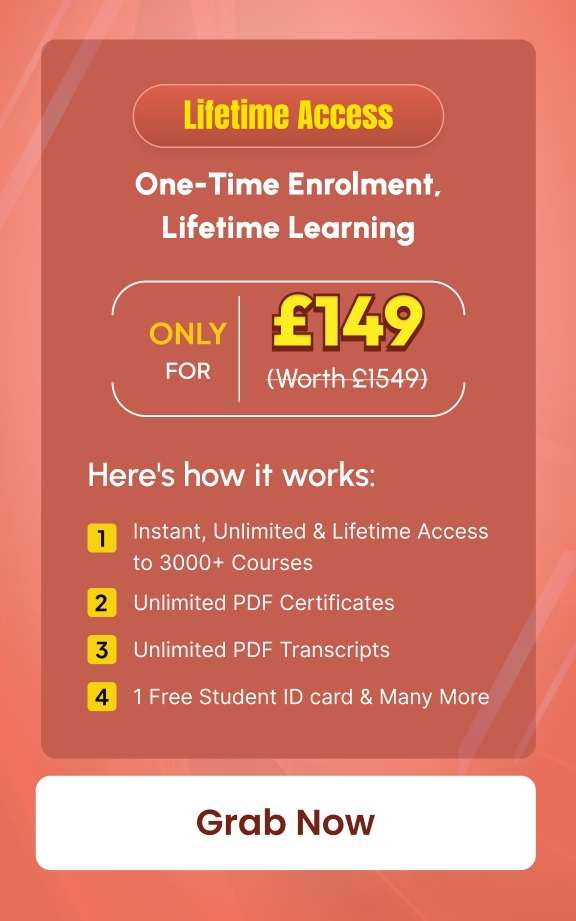
- Unlimited access to the course for a lifetime.
- Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course.
- Structured lesson planning in line with industry standards.
- Immerse yourself in innovative and captivating course materials and activities.
- Assessments are designed to evaluate advanced cognitive abilities and skill proficiency.
- Flexibility to complete the IT Administration and Networking Course at your own pace, on your own schedule.
- Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience.
Who is this IT Administration and Networking course for?
- Aspiring IT technicians poised to commence their vocational journey.
- Office administrators aiming to incorporate IT proficiency into their skillset.
- Entrepreneurs seeking to manage their business technology needs effectively.
- Students considering a career in information technology or related fields.
- Hobbyists interested in the technical aspects of computer systems.
Career path
- IT Support Technician – £18,000 – £30,000
- Network Administrator – £22,000 – £40,000
- System Administrator – £25,000 – £50,000
- Cybersecurity Analyst – £30,000 – £65,000
- Network Engineer – £28,000 – £53,000
- IT Manager – £30,000 – £70,000
Prerequisites
This IT Administration and Networking does not require you to have any prior qualifications or experience. You can just enrol and start learning.This IT Administration and Networking was made by professionals and it is compatible with all PC’s, Mac’s, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection.
Certification
After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8.
Course Curriculum
| Software: | |||
| What is an Operating System | 00:48:00 | ||
| Configuring the Operating System | 00:06:00 | ||
| What is an Application | 00:10:00 | ||
| Using Control Panel | 00:18:00 | ||
| Software and Concepts | 00:11:00 | ||
| Licensing | 00:06:00 | ||
| Using Software | 00:07:00 | ||
| Software Tools | 00:10:00 | ||
| Software | 00:14:00 | ||
| Hardware, Devices, and Peripherals | 00:05:00 | ||
| Hardware: | |||
| Hardware and Peripherals | 00:07:00 | ||
| Storage | 00:12:00 | ||
| Connectivity Devices | 00:05:00 | ||
| Network Components | 00:09:00 | ||
| Identify the Importance of Risk Management | 00:11:00 | ||
| Assess Risk | 00:13:00 | ||
| Mitigate Risk | 00:24:00 | ||
| Integrate Documentation into Risk Management | 00:15:00 | ||
| Classify Threats and Threat Profiles | 00:08:00 | ||
| Perform Ongoing Threat Research | 00:13:00 | ||
| Resources that Aid in Research of Threats | 00:03:00 | ||
| Implement Threat Modeling | 00:10:00 | ||
| Assess the Impact of Reconnaissance Incidents | 00:11:00 | ||
| Performing Reconnaissance on a Network | 00:07:00 | ||
| Examining Reconnaissance Incidents | 00:08:00 | ||
| Assess the Impact of Social Engineering | 00:11:00 | ||
| Assessing the impact of Social Engineering | 00:08:00 | ||
| Assessing the Impact of Phishing | 00:03:00 | ||
| Types of Wireless Attacks | 00:30:00 | ||
| Intrusion Monitoring | 00:08:00 | ||
| Wireless Security Risks | 00:22:00 | ||
| Authentication Attacks | 00:21:00 | ||
| Rogue Devices | 00:04:00 | ||
| Public Hotspots | 00:07:00 | ||
| Wireless Security Monitoring | 00:21:00 | ||
| Device Tracking | 00:18:00 | ||
| WLAN Security Infrastructure | 00:38:00 | ||
| Management Protocols | 00:23:00 | ||
| Other RADIUS Solutions | 00:16:00 | ||
| Security: | |||
| Introduction | 00:30:00 | ||
| Child Safety Online | 01:00:00 | ||
| Secure Payment Sites | 01:00:00 | ||
| Online Banking | 00:30:00 | ||
| How To Keep Your Password Safe | 00:30:00 | ||
| Common Scams | 01:00:00 | ||
| How I Got Pharmed | 01:00:00 | ||
| Virus Protection | 01:00:00 | ||
| Self Maintenance | 00:30:00 | ||
| Personal Information Online | 01:00:00 | ||
| Is The Internet Safe? | 00:30:00 | ||
| Importance of Cyber Security | 00:30:00 | ||
| Spyware Can Destroy | 00:30:00 | ||
| How Does Spyware Spread? | 01:00:00 | ||
| How To Remove Spyware | 01:00:00 | ||
| Anti Spyware Program | 01:00:00 | ||
| The Anti Anti-Spyware Programs | 00:30:00 | ||
| Research And Learn More | 00:30:00 | ||
| Choosing The Best Anti Spyware Tool | 01:00:00 | ||
| Computer Security And Spyware | 01:00:00 | ||
| The Programs To Avoid | 00:15:00 | ||
| Is It Legal? | 00:30:00 | ||
| Checklist Of Protection | 00:15:00 | ||
| The Information Security Cycle | 00:37:00 | ||
| Information Security Controls | 00:36:00 | ||
| Authentication Methods | 00:09:00 | ||
| Cryptography Fundamentals | 00:56:00 | ||
| Security Policy Fundamentals | 00:11:00 | ||
| Social Engineering | 00:32:00 | ||
| Malware | 00:25:00 | ||
| Software-Based Threats | 00:22:00 | ||
| Based Threats | 00:39:00 | ||
| Wireless Threats and Vulnerabilities | 00:43:00 | ||
| Physical Threats and Vulnerabilities | 00:09:00 | ||
| Manage Data Security | 00:47:00 | ||
| Manage Application Security | 00:55:00 | ||
| Manage Device and Host Security | 01:08:00 | ||
| Manage Mobile Security | 00:10:00 | ||
| A Risk Analysis | 00:17:00 | ||
| Implement Vulnerability Assessment Tools and Tchniques | 00:05:00 | ||
| Scan for Vulnerabilities | 00:27:00 | ||
| Mitigation and Deterrent Techniques | 00:19:00 | ||
| Respond to Security Incidents | 00:23:00 | ||
| Recover from a Security Incident | 00:10:00 | ||
| Networking: | |||
| OSI Layers | 00:44:00 | ||
| LANs and WANs | 00:14:00 | ||
| Network Types | 00:07:00 | ||
| Transmissions | 00:36:00 | ||
| Cables | 00:41:00 | ||
| Fiber Optics | 00:17:00 | ||
| Converters and Connectors | 00:27:00 | ||
| Wireless Security | 00:15:00 | ||
| Authentication.prproj | 00:21:00 | ||
| Wireless Security Threats | 00:30:00 | ||
| TACACS | 00:10:00 | ||
| Keys | 00:26:00 | ||
| RADIUS | 00:07:00 | ||
| VPN Technologies | 00:16:00 | ||
| Tunneling Protocols.prproj | 00:05:00 | ||
| Acceptable Use | 01:00:00 | ||
| Common Problems | 00:32:00 | ||
| Troubleshooting | 00:27:00 | ||
| Network Technician Tools | 00:46:00 | ||
| Physical and Logical Issues | 00:19:00 | ||
| Open or Closed Ports | 00:09:00 | ||
| ARP Issues | 00:13:00 | ||
| Basic IT Literacy: | |||
| Core Concepts in Healthcare IT | 00:06:00 | ||
| EMR EHR Issues | 00:05:00 | ||
| Regulations, Standards, and Stakeholders | 00:14:00 | ||
| HIPAA Controls and Compliance | 00:08:00 | ||
| Roles and Responsibilities | 00:10:00 | ||
| Manage Communication and Ethics Issues | 00:15:00 | ||
| Legal Best Practices, Requirements, and Documentation | 00:09:00 | ||
| Medical Document Imaging | 00:04:00 | ||
| Sanitation Management | 00:03:00 | ||
| Computing Essentials | 00:05:00 | ||
| Networking | 00:33:00 | ||
| Manage Servers and Software | 00:27:00 | ||
| Hardware Support | 00:14:00 | ||
| Set Up a Workstation | 00:08:00 | ||
| Troubleshoot Basic IT Issues | 00:15:00 | ||
| Troubleshoot Medical IT Issues | 00:20:00 | ||
| Implementation of an EMR EHR System | 00:34:00 | ||
| Change Control | 00:08:00 | ||
| Manage Physical and Logical Security | 00:36:00 | ||
| Implement Security Best Practices and Threat Mitigation Techniques | 00:13:00 | ||
| Manage Remote Access | 00:06:00 | ||
| Manage Wireless Security | 00:15:00 | ||
| Perform Backups and Disaster Recovery | 00:16:00 | ||

Related Courses
Step into the complex and fast-evolving world of GDPR Compliance, where data privacy meets the law of the digital age. …
0
Overview A powerful online presence can turn an ordinary accounting business into a trusted, client-attracting brand — and this course …
35
Step into the world of cloud applications with confidence through the Salesforce Heroku Masterclass, a structured guide to understanding one …
2
Grab This Course for
$557.70 Original price was: $557.70.$26Current price is: $26. ex Vat
-
 Level: Intermediate
Level: Intermediate
-
 Duration: 2 days, 1 hour
Duration: 2 days, 1 hour -
 Students: 9
Students: 9
.png)