- Home
- Course
- IT & Software
- Website Hacking From Scratch
Website Hacking From Scratch
Embark on a riveting expedition into the realm of website security with our course, “Website Hacking From Scratch.” Delve deep into the labyrinth of potential vulnerabilities, from SQL injections to XSS vulnerabilities, equipping yourself with the prowess to identify and safeguard against digital threats. By course end, learners are not only conversant with the anatomy of website vulnerabilities but are also adept at leveraging tools like Owasp ZAP for holistic website fortification.
Learning Outcomes
- Gain comprehensive insights into the foundation of website vulnerabilities and their exploitation.
- Understand and identify risks associated with file uploads, code executions, and session management.
- Acquire proficiency in detecting and safeguarding against SQL and XSS vulnerabilities.
- Master the use of automated tools, such as Owasp ZAP, in vulnerability detection.
- Develop strategies for effective post-exploitation management.
Why choose this Website Hacking From Scratch course?
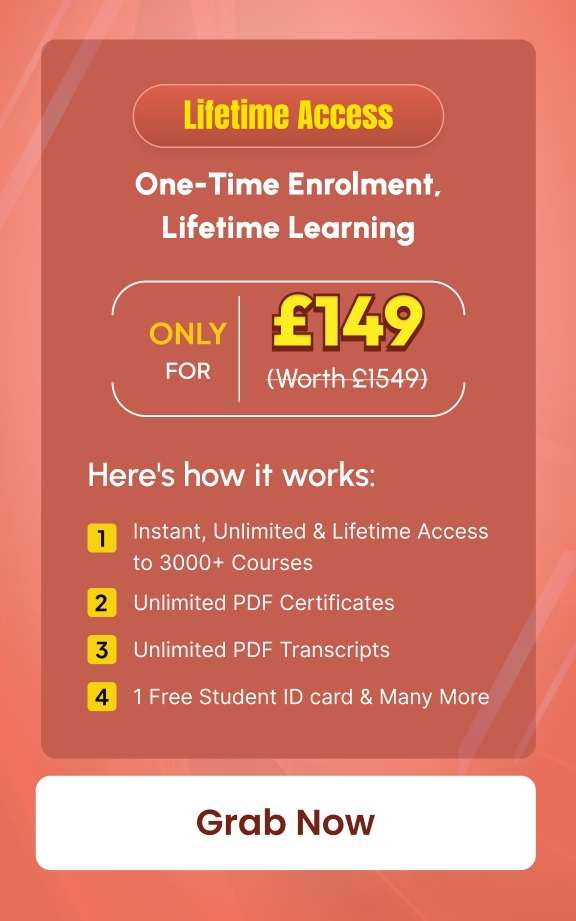
- Unlimited access to the course for a lifetime.
- Opportunity to earn a certificate accredited by the CPD Quality Standards after completing this course.
- Structured lesson planning in line with industry standards.
- Immerse yourself in innovative and captivating course materials and activities.
- Assessments are designed to evaluate advanced cognitive abilities and skill proficiency.
- Flexibility to complete the Website Hacking From Scratch Course at your own pace, on your own schedule.
- Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience.
Who is this Website Hacking From Scratch course for?
- Aspiring cybersecurity enthusiasts eager to delve into website security.
- Web developers keen to fortify their sites against potential breaches.
- IT professionals aiming to enhance their repertoire with security expertise.
- Entrepreneurs looking to ensure the robustness of their online platforms.
- Individuals curious about ethical hacking and its applications.
Career path
- Ethical Hacker: £25,000 – £70,000
- Penetration Tester: £30,000 – £60,000
- Cybersecurity Analyst: £28,000 – £55,000
- IT Security Consultant: £35,000 – £75,000
- Web Security Manager: £40,000 – £80,000
- Information Security Officer: £45,000 – £85,000
Prerequisites
This Website Hacking From Scratch does not require you to have any prior qualifications or experience. You can just enrol and start learning.This Website Hacking From Scratch was made by professionals and it is compatible with all PC’s, Mac’s, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection.
Certification
After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8.
Course Curriculum
| Course Introduction | |||
| Course Introduction | 00:02:00 | ||
| Preparation - Creating a Penetration Testing Lab | |||
| Lab Overview & Needed Software | 00:08:00 | ||
| Installing Kali 2019 As a Virtual Machine Using a Ready Image | 00:10:00 | ||
| Installing Kali 2019 As a Virtual Machine | 00:10:00 | ||
| Installing Metasploitable As a Virtual Machine | 00:04:00 | ||
| Preparation - Linux Basics | |||
| Basic Overview of Kali Linux | 00:05:00 | ||
| The Linux Terminal & Basic Linux Commands | 00:11:00 | ||
| Configuring Metasploitable & Lab Network Settings | 00:06:00 | ||
| Website Basics | |||
| What is a Website? | 00:04:00 | ||
| How To Hack a Website? | 00:04:00 | ||
| Information Gathering | |||
| Gathering Information Using Whois Lookup | 00:05:00 | ||
| Discovering Technologies Used On The Website | 00:06:00 | ||
| Gathering Comprehensive DNS Information | 00:10:00 | ||
| Discovering Websites On The Same Server | 00:04:00 | ||
| Discovering Subdomains | 00:12:00 | ||
| Discovering Sensitive Files | 00:07:00 | ||
| Analysing Discovered Files | 00:04:00 | ||
| Maltego – Discovering Servers, Domains & Files | 00:08:00 | ||
| Maltego – Discovering Websites, Hosting Provider & Emails | 00:05:00 | ||
| File Upload Vulnerabilities | |||
| What are they? And How To Discover & Exploit Basic File Upload Vulnerabilities | 00:07:00 | ||
| HTTP Requests – GET & POST | 00:04:00 | ||
| Intercepting HTTP Requests | 00:07:00 | ||
| Exploiting More Advanced File Upload Vulnerabilities | 00:04:00 | ||
| Exploiting More Advanced File Upload Vulnerabilities | 00:04:00 | ||
| [Security] Fixing File Upload Vulnerabilities | 00:06:00 | ||
| Code Execution Vulnerabilities | |||
| What are they? & How To Discover & Exploit Basic Code Execution Vulnerabilities | 00:07:00 | ||
| Exploiting Advanced Code Execution Vulnerabilities | 00:06:00 | ||
| [Security] – Fixing Code Execution Vulnerabilities | 00:06:00 | ||
| Local File Inclusion Vulnerabilities (LFI) | |||
| What are they? And How To Discover & Exploit Them | 00:06:00 | ||
| Gaining Shell Access From LFI Vulnerabilities – Method 1 | 00:07:00 | ||
| Gaining Shell Access From LFI Vulnerabilities – Method 2 | 00:11:00 | ||
| Remote File Inclusion Vulnerabilities (RFI) | |||
| Remote File Inclusion Vulnerabilities – Configuring PHP Settings | 00:04:00 | ||
| Remote File Inclusion Vulnerabilities – Discovery & Exploitation | 00:06:00 | ||
| Exploiting Advanced Remote File Inclusion Vulnerabilities | 00:03:00 | ||
| [Security] Fixing File Inclusion Vulnerabilities | 00:06:00 | ||
| SQL Injection Vulnerabilities | |||
| What is SQL | 00:06:00 | ||
| Dangers of SQL Injections | 00:03:00 | ||
| SQL Injection Vulnerabilities - SQLi In Login Pages | |||
| Discovering SQL Injections In POST | 00:08:00 | ||
| Bypassing Logins Using SQL Injection Vulnerability | 00:05:00 | ||
| Bypassing More Secure Logins Using SQL Injections | 00:06:00 | ||
| [Security] Preventing SQL Injections In Login Pages | 00:08:00 | ||
| SQL Injection Vulnerabilities - Extracting Data From The Database | |||
| Discovering SQL Injections in GET | 00:07:00 | ||
| Reading Database Information | 00:05:00 | ||
| Finding Database Tables | 00:04:00 | ||
| Extracting Sensitive Data Such As Passwords | 00:04:00 | ||
| SQL Injection Vulnerabilities - Advanced Exploitation | |||
| Discovering & Exploiting Blind SQL Injections | 00:06:00 | ||
| Discovering a More Complicated SQL Injection | 00:07:00 | ||
| Extracting Data (passwords) By Exploiting a More Difficult SQL Injection | 00:05:00 | ||
| Bypassing Filters | 00:05:00 | ||
| Bypassing Security & Accessing All Records | 00:09:00 | ||
| [Security] Quick Fix To Prevent SQL Injections | 00:07:00 | ||
| Reading & Writing Files On The Server Using SQL Injection Vulnerability | 00:06:00 | ||
| Getting A Reverse Shell Access & Gaining Full Control Over The Target Web Server | 00:08:00 | ||
| Discovering SQL Injections & Extracting Data Using SQLmap | 00:07:00 | ||
| [Security] – The Right Way To Prevent SQL Injection | 00:05:00 | ||
| XSS Vulnerabilities | |||
| Introduction – What is XSS or Cross Site Scripting? | 00:03:00 | ||
| Discovering Basic Reflected XSS | 00:04:00 | ||
| Discovering Advanced Reflected XSS | 00:05:00 | ||
| Discovering An Even More Advanced Reflected XSS | 00:07:00 | ||
| Discovering Stored XSS | 00:03:00 | ||
| Discovering Advanced Stored XSS | 00:04:00 | ||
| XSS Vulnerabilities - Exploitation | |||
| Hooking Victims To BeEF Using Reflected XSS | 00:06:00 | ||
| Hooking Victims To BeEF Using Stored XSS | 00:04:00 | ||
| BeEF – Interacting With Hooked Victims | 00:04:00 | ||
| BeEF – Running Basic Commands On Victims | 00:04:00 | ||
| BeEF – Stealing Credentials/Passwords Using A Fake Login Prompt | 00:02:00 | ||
| Bonus – Installing Veil 3.1 | 00:06:00 | ||
| Bonus – Veil Overview & Payloads Basics | 00:07:00 | ||
| Bonus – Generating An Undetectable Backdoor Using Veil 3 | 00:10:00 | ||
| Bonus – Listening For Incoming Connections | 00:07:00 | ||
| Bonus – Using A Basic Delivery Method To Test The Backdoor & Hack Windows 10 | 00:07:00 | ||
| BeEF – Gaining Full Control Over Windows Target | 00:04:00 | ||
| [Security] Fixing XSS Vulnerabilities | 00:07:00 | ||
| Insecure Session Management | |||
| Logging In As Admin Without a Password By Manipulating Cookies | 00:06:00 | ||
| Discovering Cross Site Request Forgery Vulnerabilities (CSRF) | 00:07:00 | ||
| Exploiting CSRF Vulnerabilities To Change Admin Password Using a HTML File | 00:07:00 | ||
| Exploiting CSRF Vulnerabilities To Change Admin Password Using Link (Preview) | 00:06:00 | ||
| [Security] The Right Way To Prevent CSRF Vulnerabilities | 00:09:00 | ||
| Brute Force & Dictionary Attacks | |||
| What Are Brute Force & Dictionary Attacks? | 00:04:00 | ||
| Creating a Wordlist | 00:07:00 | ||
| Launching a Wordlist Attack & Guessing Login Password Using Hydra | 00:14:00 | ||
| Discovering Vulnerabilities Automatically Using Owasp ZAP | |||
| Scanning Target Website For Vulnerabilities | 00:04:00 | ||
| Analysing Scan Results | 00:04:00 | ||
| Post Exploitation | |||
| Post Exploitation Introduction | 00:04:00 | ||
| Interacting With The Reverse Shell Access Obtained In Previous Lectures | 00:07:00 | ||
| Escalating Reverse Shell Access To Weevely Shell | 00:08:00 | ||
| Weevely Basics – Accessing Other Websites, Running Shell Commands …etc | 00:07:00 | ||
| Bypassing Limited Privileges & Executing Shell Commands | 00:05:00 | ||
| Downloading Files From Target Webserver | 00:05:00 | ||
| Uploading Files To Target Webserver | 00:08:00 | ||
| Getting a Reverse Connection From Weevely | 00:08:00 | ||
| Accessing The Database | 00:09:00 | ||
| Resources | |||
| Resources – Website Hacking From Scratch | 00:00:00 | ||
| Assignment | |||
| Assignment – Website Hacking From Scratch | 00:00:00 | ||

Related Courses
In a world powered by information, understanding gdpr meaning is no longer optional—it is essential. As organisations across Britain process …
1
Step into the complex and fast-evolving world of GDPR Compliance, where data privacy meets the law of the digital age. …
0
Overview A powerful online presence can turn an ordinary accounting business into a trusted, client-attracting brand — and this course …
35
Grab This Course for
$557.70 Original price was: $557.70.$26Current price is: $26. ex Vat
-
 Level: Intermediate
Level: Intermediate
-
 Duration: 9 hours, 23 minutes
Duration: 9 hours, 23 minutes -
 Students: 242
Students: 242
.png)