- Home
- Course
- IT & Software
- Computer Hacking Forensic Investigator
Computer Hacking Forensic Investigator
The Computer Hacking Forensic Investigator course marks your entry into the intricate and compelling world of cybersecurity and digital forensics. This curriculum is crafted to guide you through the multifaceted aspects of cyber investigation, starting with a foundational overview and gradually moving into the complexities of system reconnaissance. You’ll be introduced to various protocols, diving deep into the realm of Windows hacking and the nuances of attacking web technologies. The course is a balanced mix of theory and practical application, aimed at equipping you with the skills necessary to navigate the challenging landscape of cyber forensics.
As you progress, you’ll be immersed in the world of pen testing wireless networks and the rigorous process of forensic investigation. This course is not just a learning pathway; it’s an experience that transforms you into a thinker and analyst, capable of handling the subtleties of digital evidence and artifacts. You’ll be adept at examination and analysis by the end of this journey, ready to tackle other forensics areas and manage incidents with a professional edge and strategic acumen.
Learning Outcomes
- Master the foundational principles and techniques in computer hacking and forensics.
- Develop proficiency in analyzing and responding to different hacking methods.
- Attain expertise in conducting comprehensive forensic investigations.
- Learn the art of preserving and interpreting digital evidence.
- Acquire skills in managing and responding to cybersecurity incidents effectively.
Why choose this Computer Hacking Forensic Investigator course?
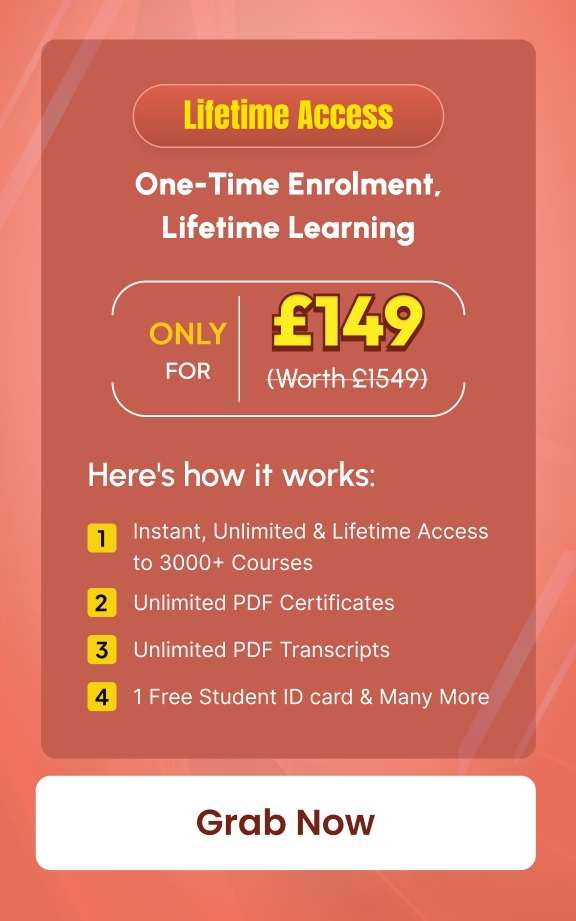
- Unlimited access to the course for a lifetime.
- Opportunity to earn a certificate accredited by the CPD Quality Standards and CIQ after completing this course.
- Structured lesson planning in line with industry standards.
- Immerse yourself in innovative and captivating course materials and activities.
- Assessments designed to evaluate advanced cognitive abilities and skill proficiency.
- Flexibility to complete the Course at your own pace, on your own schedule.
- Receive full tutor support throughout the week, from Monday to Friday, to enhance your learning experience.
- Unlock career resources for CV improvement, interview readiness, and job success.
Who is this Computer Hacking Forensic Investigator course for?
- Individuals aspiring to a career in cybersecurity and digital forensics.
- IT experts wishing to delve into the specifics of ethical hacking and cyber investigation.
- Law enforcement professionals focusing on cybercrime detection and response.
- Enthusiasts in cybersecurity, keen on understanding hacking and forensic methods.
- Security personnel in organizations seeking to protect digital infrastructures.
Career path
- Cybersecurity Analyst – £30,000 to £50,000
- Forensic Computer Analyst – £25,000 to £40,000
- Information Security Manager – £40,000 to £60,000
- Ethical Hacker – £35,000 to £55,000
- Incident Response Analyst – £30,000 to £45,000
- Digital Forensics Investigator – £35,000 to £50,000
Prerequisites
This Computer Hacking Forensic Investigator does not require you to have any prior qualifications or experience. You can just enrol and start learning. This course was made by professionals and it is compatible with all PC’s, Mac’s, tablets and smartphones. You will be able to access the course from anywhere at any time as long as you have a good enough internet connection.
Certification
After studying the course materials, there will be a written assignment test which you can take at the end of the course. After successfully passing the test you will be able to claim the pdf certificate for £4.99 Original Hard Copy certificates need to be ordered at an additional cost of £8.
Course Curriculum
| Overview | |||
| Overview | 00:35:00 | ||
| Reconnaissance | |||
| Reconnaissance | 00:25:00 | ||
| Protocols | |||
| Protocols | 01:26:00 | ||
| Windows Hacking | |||
| Windows Hacking | 01:19:00 | ||
| Attacking Web Technologies | |||
| Attacking Web Technologies | 00:56:00 | ||
| Pen Testing Wireless Networks | |||
| Pen Testing Wireless Networks | 01:34:00 | ||
| Forensic Investigation | |||
| Introduction | 00:13:00 | ||
| Computer Forensic Incidents | 00:28:00 | ||
| Examination and Analysis | |||
| Investigation Process | 00:54:00 | ||
| Disk Storage Concepts | 00:31:00 | ||
| Digital Acquisition & Analysis | 00:24:00 | ||
| Protocols | |||
| Forensic Examination Protocols | 00:25:00 | ||
| Digital Evidence Protocols | 00:21:00 | ||
| CFI Theory | 00:25:00 | ||
| Digital Evidence | |||
| Digital Evidence Presentation | 00:22:00 | ||
| Computer Forensic Laboratory Protocols | 00:33:00 | ||
| Computer Forensic Processing | 00:22:00 | ||
| Digital Forensics Reporting | 00:20:00 | ||
| Artifacts | |||
| Specialized Artifact Recovery | 00:46:00 | ||
| Discovery and ESI | 00:12:00 | ||
| Other Forensics | |||
| Cell Phone Forensics | 00:21:00 | ||
| USB Forensics | 00:06:00 | ||
| Incident Handling | |||
| Incident Handling | 00:36:00 | ||
| PDA Forensics | 00:23:00 | ||
| Investigating Harassment | 00:14:00 | ||

Grab This Course for
$557.70 Original price was: $557.70.$26Current price is: $26. ex Vat
-
 Level: Intermediate
Level: Intermediate
-
 Duration: 14 hours, 11 minutes
Duration: 14 hours, 11 minutes -
 Students: 6
Students: 6
.png)